In light of the recent news circulating about sporadic WannaCry outbreaks, namely defense contractor Boeing and earlier last month Connecticut state agencies, as well as Honda, we think it important to provide further guidance on assessing ongoing and hidden dangers related to WannaCry outbreaks.
To immediately begin reducing risk and augmenting your existing security defenses, we are providing at no cost Telltale, a free version of Vantage Breach Intelligence Feed. Telltale is a simplified version of our breach monitoring and can help your organization assess past or ongoing malware infections, including but not limited to WannaCry. We will be regularly updating Telltale with new sinkhole data from botnets and useful breach monitoring features.
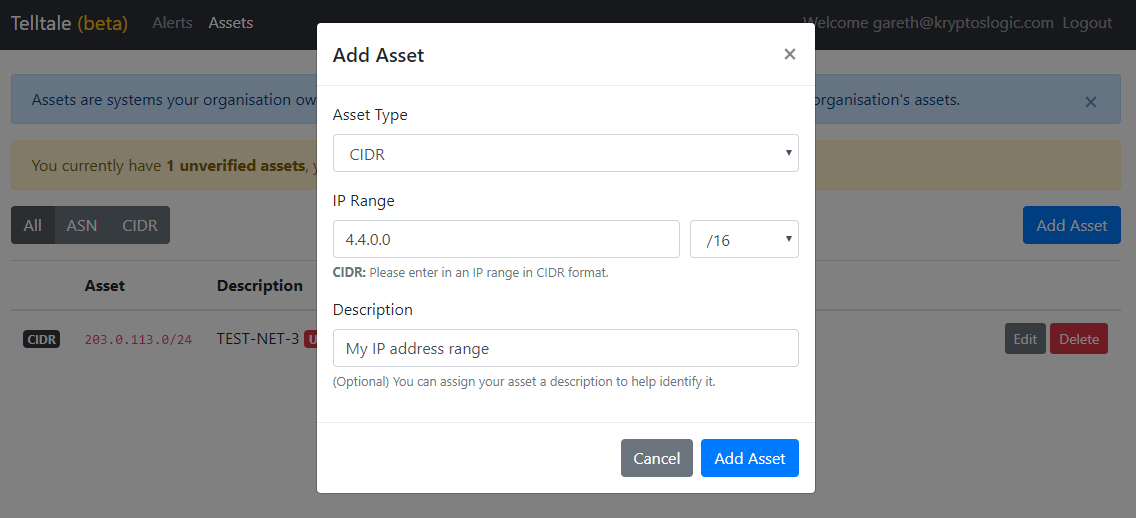
Telltale Assets.
A common misconception with WannaCry is that due to the kill-switch, or by creating your own internal kill-switch (corporate DNS, proxy, etc), systems are automatically safe from WannaCry’s ransomware propagation and payload. This assumption is categorically false, and WannaCry is still very much active. We have observed approximately 100 million connection attempts, from 2.7 million unique IPs, on the kill-switch over the period of March 2018. This has been the trend for almost a year with little sign of slowing down.
We estimate a wide variety of hundreds of thousands of untreated and dormant Microsoft Windows infections maintain a foothold and are responsible for the residual and continued propagation of WannaCry, which by our dataset analysis and estimates reach several (potentially tens of) million systems through an ebb and flow infection cycle every month.
Unfortunately, as various organizations have discovered, there are a number of scenarios where WannaCry still poses a serious threat. This post will help demystify some of these scenarios and detail what you can do to predict and prevent an outbreak within your environment.
Updating your ransomware scenario Threat Models
If your organization has chosen to defer risks and not apply relevant patches to all systems, you are definitely not alone. However, it is crucial to understand at least two common scenarios your organization may be affected by existing threat cycles, some which may not be obvious due to the complex nature of this threat.
Scenario 1: One or more of your unpatched devices can be reached by an infected system and relies on the Internet based Kryptos kill-switch to prevent WannaCry.
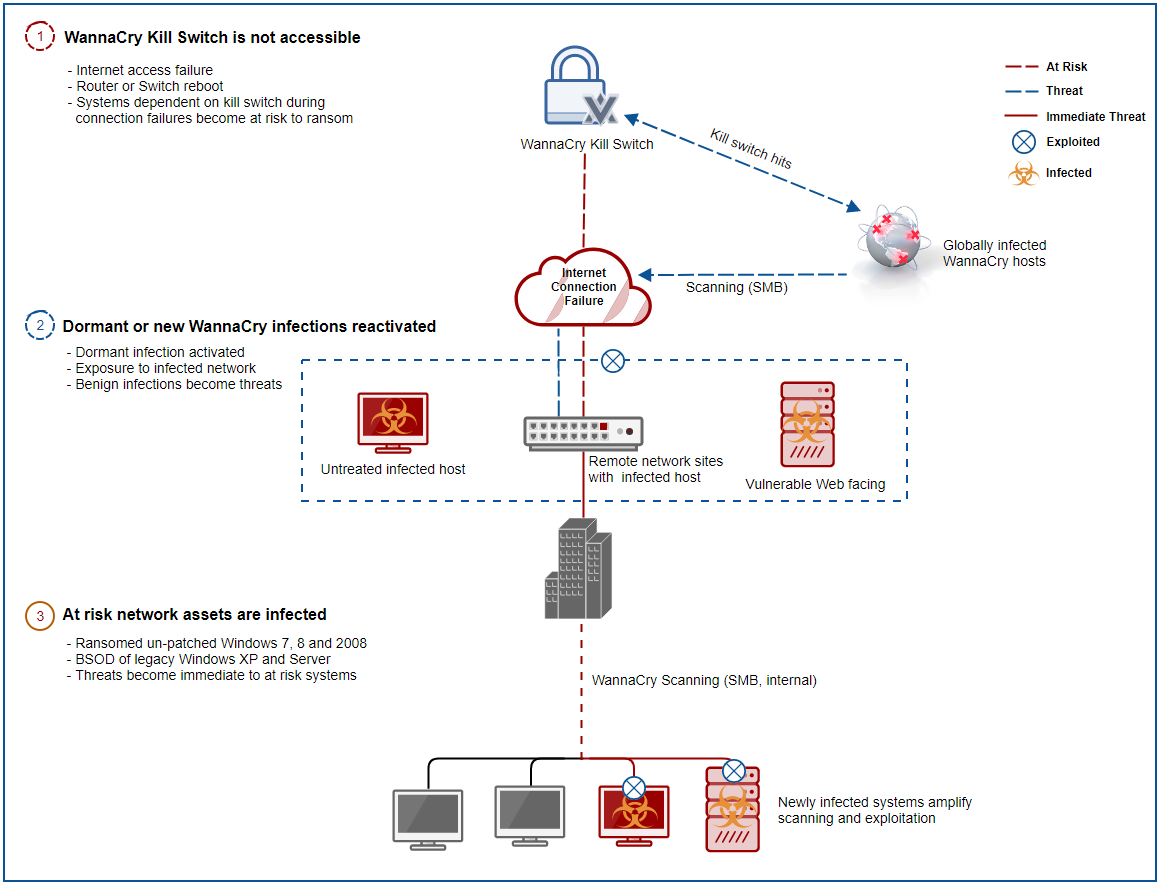
SMB WannaCry Threat Scenario (click to enlarge)
In this scenario, which is most common to small and medium sized businesses (SMBs), if the following conditions are met you are very likely to activate a WannaCry outbreak:
- Condition 1: Any network asset such as an ISP, router, endpoint, or switch is rebooted, misconfigured, fails or otherwise loses connectivity;
- Condition 2: You have a dormant or existing infection somehow adjacent to your assets or a vulnerable server facing the public Internet;
- Condition 3: There is at least one unpatched system within your environment which is vulnerable to EternalBlue.
Scenario 2: One or more of your unpatched devices in an enterprise can be reached by an infected system relying on a proxy or DNS to prevent WannaCry, instead of the Kryptos kill-switch.
In this scenario, which is more common in large enterprises, if the following conditions are met it is very likely to enable a WannaCry outbreak:
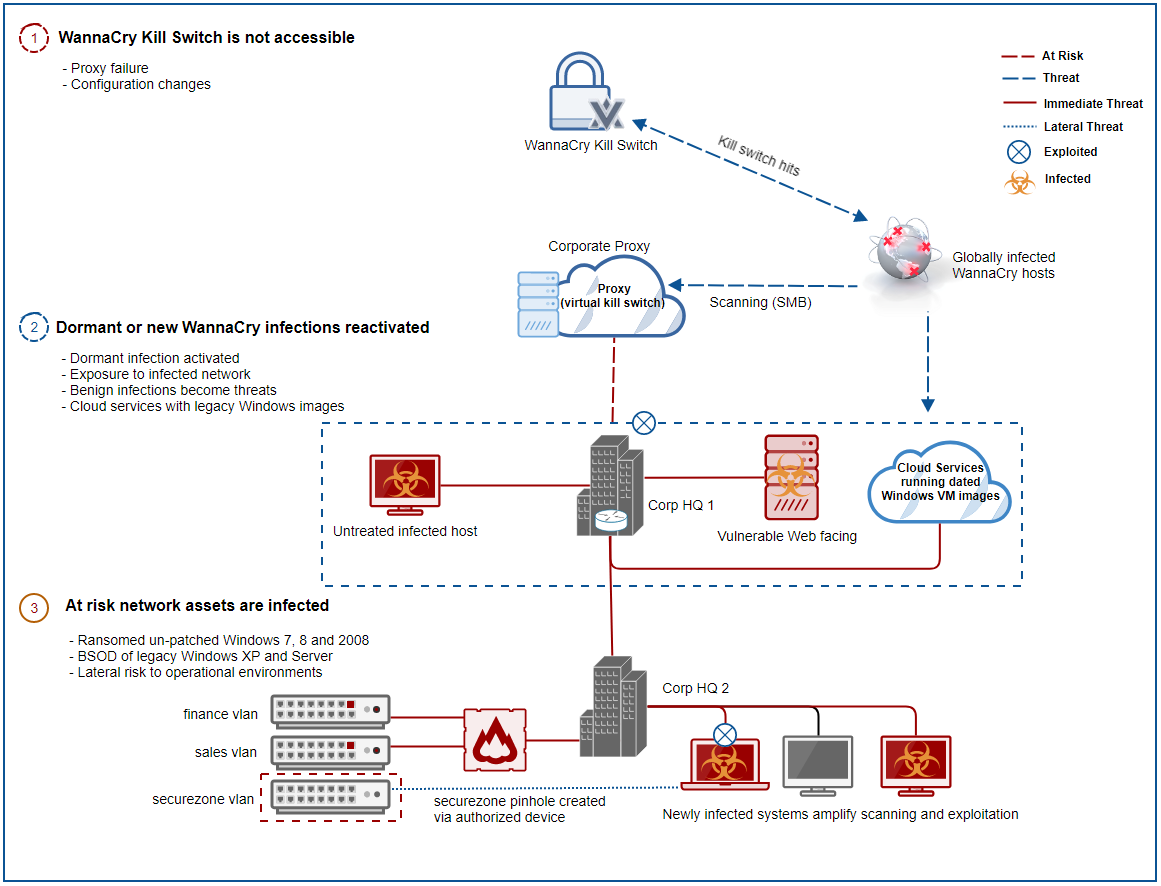
Enterprise WannaCry Threat Scenario (click to enlarge)
- Condition 1: Corporate proxy internal DNS is rebooted or fails (rule change, update, etc)
- Condition 2: Part of your network segmentation fails due to firewall changes or new routes are introduced
- Condition 3: Infection propagates through network and reaches adjacent VLANs
Note: If adjacent VLANs were never intended to connect to corporate proxies, such as an air-gap, then it would leave this network completely exposed to full impact, as there is no internal DNS kill-switch or Internet connectivity to Kryptos Logic’s kill-switch. Unfortunately, this is one of the most common operational technology scenarios that have yet to be tested or mitigated. Using Kryptos Logic’s threat simulation module could be an effective way to determine if these environments could be at risk of an exposure to any of the above scenarios.
Preventative steps for addressing lingering WannaCry or EternalBlue risks
If available or where possible, perform as many of these steps to determine your current awareness with an internal WannaCry assessment:
- Sign up for Telltale, determine if your IP address range is part of the WannaCry datasets. Monitor for alerts regularly.
- Parse your proxy or web filter logs files for hits to the primary kill-switch domain
iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.comand, where possible, any other extended kill-switch domains which were discovered. - Parse anti-virus log files for quarantined threats related to EternalBlue/WannaCry. Determine source of attack.
- Scan your environment (vulnerability scanner,
nmap, etc) for vulnerable SMB services, where possible apply Windows patches. - Scan endpoints for indicators of compromise associated with the ransomware and ensure there are no dormant infections which can be triggered.
- Configure a rule in your proxy or DNS such that if the kill-switch(s) are contacted an alert is generated. This can be particularly helpful when new assets hosting infections are introduced to the environment.
- Consider step #6 in your secured or air-gapped environments. Assuming pinholes will never be created is too a high risk to leave to chance. This step can save your environment from serious impacts, if implemented correctly, especially where patching may not be feasible in certain circumstances.
Avoid assumptions about the assessment results as they can be incomplete. For instance, “We have checked our proxy logs for the last 30 days and there are no kill-switch hits.” WannaCry infected systems will scan for an initial 24 hours before settling into an indefinite dormant state, the scan sequence will repeat again when the a system is inevitably rebooted. Another common observation, “Our antivirus caught the infection so we are safe.” Chances are the quarantine event was due to external exploitation sourced from a different infected device, thus the root cause is still unresolved. And of course, “There is a kill-switch, so the threat is mitigated.” Any single point of failure in the resolution of the domain considerably exposes your organization at that time to an uncontrolled outbreak.
Conclusion
Because of the aggressive and persistent design of WannaCry, even seemingly mitigated networks remain at risk. Smaller networks and endpoints with fewer defense resources should consider a reliable DNS such as Cloudflare’s newly-announced privacy friendly DNS and ensuring Windows Updates were applied. Larger enterprises ultimately need to engage in removing systemic risks and patch.
To be clear, an enterprise with no detectable WannaCry infections can still be reasonably susceptible to an outbreak at any given moment if patching is incomplete. The perfect storm exists where endpoints have no AV installed and Windows is not updated, ironically, this is quite typical of the most critical production environments. Organizations most at risk are those unaware of hosting residual infections and which operate unpatched adjacent systems.
A key takeaway is millions of actively infected WannaCry devices continue to relentlessly work to infect unpatched Windows systems. Most of these attack efforts go unnoticed due to the kill-switch and corporate proxy’s mitigating the ransom payload. However, any number of common failures can result in an outbreak, one where the ransom payload will not be mitigated. To bolster new or existing efforts against these threats, organizations can immediately reduce their risks and obtain actionable intelligence about their current exposure to WannaCry and other botnets by subscribing to the sinkhole dataset from our breach monitoring platform Telltale and following the prescribed preventative steps.
