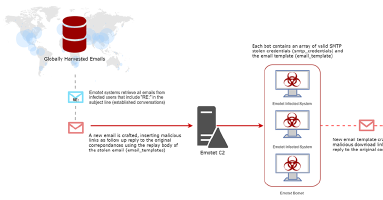
Emotet scales use of stolen email content for context-aware phishing
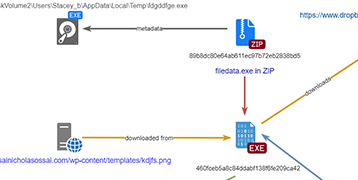
Emotet’s automated targeting phishing campaigns have arrived and they are aggressive. As originally discovered and predicted in our previous post about Emotet’s mass email harvesting, computers infected with Emotet and the email harvesting module could be used to create believable emails which even savvy email users may be tricked into clicking. Since then, Kryptos’ Threat Intelligence Team has observed Emotet’s behavior evolve, with the aid of their stolen email troves. During the past few days in particular, we have spotted the Emotet actors implement a new process allowing them to automate and scale the use of targeted emails.